UniFi, VLANs, Sonos and igmp-proxy
As an exercise in good network health, I spent some time last month moving all the “Internet of Things” devices in my network onto their own segregated VLAN. I’ve configured things so that by default no traffic can leave the IoT network without my adding explicit rules to permit it. This protects the trusted side of my network from potentially dodgy traffic from the IoT devices with cheap WiFi chips and Chinese hosted servers. (I’m looking at you ThermoGroup.)
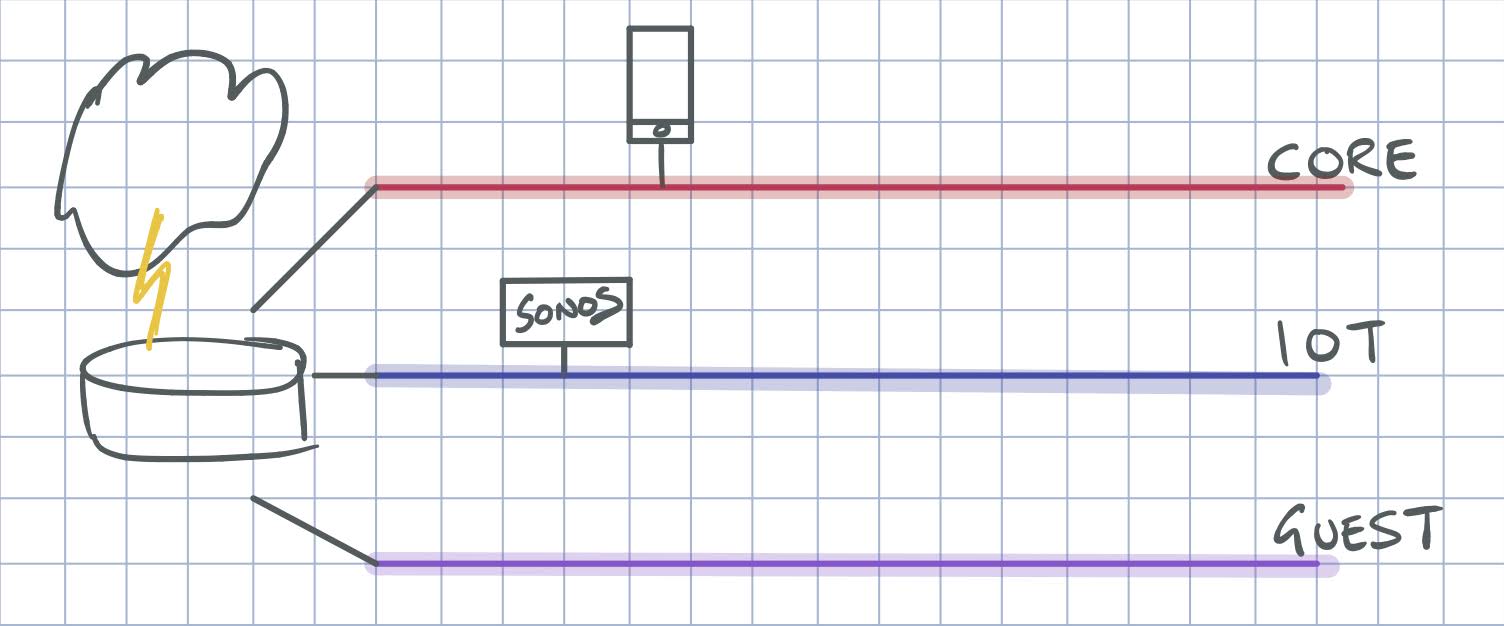
Logically, my network ends up looking something like this, with separate networks for the trusted kit, the IoT devices and the guest wireless network.
One wrinkle with this approach is that – by design – each VLAN is its own broadcast domain. That means the devices on my primary trusted VLAN can no longer use multicast to discover devices on the IoT VLAN. The most obvious victim of this was Sonos – none of the controllers could see the Sonos devices once I separated the LANs. Enter igmpproxy running on my router – the UniFi USG-PRO-4.
From the man page for igmpproxy:
igmpproxy is a simple multicast routing daemon which uses IGMP forwarding to dynamically route multicast traffic. Routing is done by defining an “upstream” interface on which the daemon act as a normal Multicast client, and one or more “downstream” interfaces that serves clients on the destination networks.
I run this on the USG-PRO-4 and configure it to proxy between the IoT and Core VLANs. In this way the Sonos controllers on the core network can see the devices on the IoT VLAN. This isn’t exposed in the UniFi UI, so I alter the config.gateway.json on the controller with this config:
{
"protocols": {
"igmp-proxy": {
"interface": {
"eth0": {
"role": "upstream",
"threshold": "1"
},
"eth0.105": {
"role": "downstream",
"threshold": "1"
}
}
}
}
}
Here eth0 represents my core VLAN, and eth0.105 is the tag on my IoT LAN. This config gets saved to the sites directory on the controller. On my Cloud Key Gen 2 Plus this is /srv/unifi/data/sites/default/. There are more details in the Ubiquiti article on the subject. Use the UI to force provision the router and this config will get added.
And now we crash.
This worked well – in fact my Sonos controller on the Mac immediately refreshed to show all the Sonos devices in the house. Then a few days later it suddenly stopped working. Checking the router showed that igmp-proxy had stopped running.
This happens often enough that I needed a script to run regularly to see if the proxy had stopped and if so, start it again:
#!/bin/bash
pidof igmpproxy >/dev/null
if [[ $? -ne 0 ]] ; then
echo "restarting igmp-proxy"
/bin/vbash -ic 'restart igmp-proxy'
fi
I saved this to /config/igmpcheck.sh on the router itself. To get it running regularly, we need to add another config to the config.gateway.json, to enable a task scheduler:
"system": {
"task-scheduler": {
"task": {
"igmpcheck": {
"executable": {
"path": "/config/igmpcheck.sh"
},
"interval": "5m"
}
}
}
}
Again, force provision the router so the config loads. Since I added this I’ve not noticed the brief periods where igmp-proxy fails.
It’d be nice to see the task scheduler and indeed igmp-proxy settings exposed in the UniFi UI. Ubiquiti are adding stuff all the time – the UI is getting more fully featured with every release – so I imagine it will come eventually.
Enjoy Reading This Article?
Here are some more articles you might like to read next: